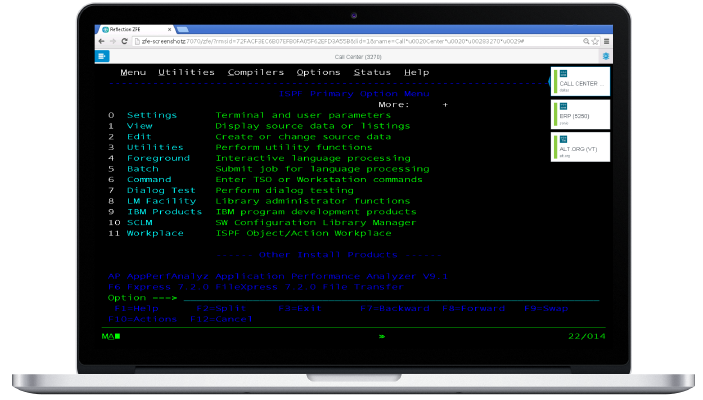
Deliver browser-based, HTML5 access to 3270, 5250, VT, Unisys and Airline host application sessions from a central location—without the need to touch the desktop or manage Java runtime environments. Protect communications with HTTPS, SSL/TLS, and SSH security.
Provide secure access to your host systems using your existing identity management solution. With Active Directory/LDAP integration, easily entitle emulation sessions to trusted end users.
With centralized administration, control user access to mainframe applications from a single web-based console. Quickly confirm that a user has been authenticated and granted access to a host session before that session is ever allowed—and keep your sensitive host data secure.
Use centralized activity logging to identify which users are accessing your host systems and the total number of sessions connecting to the host. With the metering tool, you can monitor and report on user and session volumes and optimize how you allocate computing resources and provision user access rights.
Easily deliver zero-footprint terminal emulation across the enterprise without the need to manage desktop software.
Define and provision emulation sessions, control user access to mainframe applications, and monitor usage—all from a single, central point of administration.
Leverage centralized metering and reporting to optimize computing resource allocation and track user access.
Streamline and secure your host-access operation by teaming Reflection®, Extra!®, Rumba+®, or InfoConnect with MSS. Working with your Identity and Access Management (IAM) system, MSS seamlessly propagates changes to application settings and user-specific content from a central server. Next time users launch a session, they’ll receive the changes.
Manage host-access operations from your central MSS console. Lock down 100s (or 1000s) of far-flung desktops with ease. Grant or deny access based on group or role. Apply changes quickly to align with business needs. Make post-install adjustments on the fly. Do it on your schedule, not someone else’s.
Finally, you can bring your host into the IAM fold. That means you can replace weak, eight-character passwords with strong, complex ones. Implement best-fit multifactor authentication methods. Say goodbye to host passwords and automatically sign users on to their mainframe applications. It’s safe, manageable, and economical with MSS.